Fetch-Decode-Execute Model:
Arithmetic/logic unit (ALU): The part of the CPU that does calculations and logic operations is called the arithmetic/logic unit (ALU).
Inside the CPU are several memory locations called registers. These are extremely fast to access, but there are usually only a relatively small number of them. Some registers play a specific role in the fetch-decode-execute cycle, for example, holding a memory address, an instruction, or a piece of data, while others serve a general purpose.
Some of the registers with a specific role that are found in most computers include the following:
- The accumulator holds the results of calculations performed by the ALU. (All input and output from the CPU passes through the accumulator.)
- The program counter holds the memory address of the next instruction to be fetched.
- Current Instructions (holds the instruction currently being executed.)
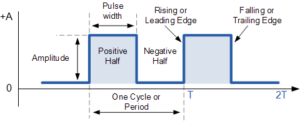
The steps in the cycle are controlled by a control unit and synchronized by an electronic clock. You have probably seen the advertised clock speeds of CPUs; for example, a 2.2 GHz CPU means that its clock ticks 2200 million times per second.
The bus that connects the CPU to other devices in the computer is split into three parts: the address bus, the data bus, and the control bus.
- The address bus carries memory addresses between the CPU and memory to identify uniquely a memory location.
- The data bus carries the value to be read from or written to memory, and
- The control bus carries the signals that, for example, determine whether to read or write the data and when to do so.
Fetch-Decode-Execute Cycle:
- The processor checks the program counter to see which instruction to run next.
- The program counter gives an address value in the memory of where the next instruction is.
- The processor fetches the instruction value from this memory location.
- Once the instruction has been fetched, it needs to be decoded and executed. For example, this could involve taking one value, putting it into the ALU, then taking a different value from a register and adding the two together.
- Once this is complete, the processor goes back to the program counter to find the next instruction.
- This cycle is repeated until the program ends.